How A Real Research Quest Led To An Absurd Story
If you have followed the Qanon conspiracy phenomenon, or any of the Q-adjacent conspiracists, you’ve no doubt read about, or heard of, the U.S. Military raid on a SCYTL facility in Frankfurt, Germany, in order to seize a SCYTL server that held the much-needed proof of election fraud in the 2020 U.S. election. You may have read my research into this story where I traced the origins of the conspiracy theory to its source. That research was included in Jack Murphy’s article titled, Origins of the Conspiracy of the 305th Military Intelligence Battalion.
Most of the direct links within that article are no longer valid. Many of the Qanon followers had their social media accounts deleted by the various social media companies soon after the chaos at the U.S. Capitol on 6 JAN 21. As a result, the subject of that conspiracy theory tracking research and his posts on the subject are now gone from Facebook, where it all began. Because of that, I thought I would author this report in order to show how the tracking was done, what it revealed, and show you the original posts. All of the information was saved and stored, giving me the ability to provide more detail.
Not satisfied with simply adding more information or providing the now-deleted posts as context, I went a step further. Perhaps three or four steps. I tracked down the source, not only of the Server Raid story itself, but of the information used to create it. This piece will contain all of that information in one handy location. Links are provided where possible. Screenshots taken at the time of the research are used in other instances due to the content no longer being available on the original platforms.
SCYTL’s Election Reporting Software
SCYTL is an election technology company primarily involved in U.S. elections by providing various software suites for Election Night Reporting (ENR) of election results. In its simplest terms, election officials take the tabulation results as they come in during election night and those figures are sent to the ENR software which then broadcasts those results to the constituents over the web or by sending them to local news outlets throughout the night.
I want to make one thing very clear at this point: SCYTL’s ENR is receiving vote counts that have already been tabulated. This software does not accept votes as they come in and does not tabulate any votes. It is simply fed with tabulation results that are then sent out to whatever platform the area is using to display election results. Someone tampering with the ENR software could change the voting results that are being broadcast to the media and the citizenry, but it cannot change the actual votes that have been cast. Your local news channel might be displaying Candidate A being in the lead due to manipulated ENR software but the winner of the election winds up being Candidate B, who received the most votes. Actual vote counts would be unaffected.
Although manipulating this process doesn’t alter the secure votes cast, there is an argument to be made that if enough incorrect information was distributed vie ENR, it could discourage people from going to the polls to cast their own ballot. If Candidate A is showing a twenty point lead over Candidate B, going through the trouble of going to the polls when you assume the race has already been won may be less of a priority. I only note this aspect of the discussion for contrast. I am not an expert on election software. As a researcher, possibilities exist that must be addressed and there are processes we must ensure remain secure.
SCYTL being an election software company and being involved in U.S. elections automatically adds them to the conspiracy theorist’s list of Deep State Cabal organizations that are stealing elections in favor of the preferred Deep State candidate. Other companies would be Dominion Voting Systems, ES&S, Smartmatic, and Hart.
Votes Tabulated and Housed Offshore
SCYTL is an international company founded in Spain in 2001. Being an international organization, naturally they have offices and facilities in various locations around the world. Questions as to why a foreign company has any part in U.S. elections are everywhere within the conspiracy space. If you return to the SCYTL link three paragraphs above, you’ll notice the address ends in .us. This is SCYTL’s U.S. operation. In an AP Fact Check article, SCYTL explains that all U.S. related work by SCYTL is contained within the U.S. and no information is sent overseas. SCYTL’s response also explains what SCYTL’s involvement in U.S. elections amounts to. Within the AP fact checking article, SCYTL does explain the existence of a server located in Frankfurt, Germany, and why or how it was utilized in 2019. This will be central to the research revealed later in this article. For those who don’t read SCYTL’s explanation – that server was used during a UK project and was never part of any U.S. election.
Foreign Interference Conspiracies – 2019 Edition
The fear of foreign interference, as well as the occasional outright evidence of it, has been a part of our election process for as long as there has been an election process. Post 2000, however, with the ease of access to information for virtually every citizen via the internet, people weren’t just talking about it. They were determined to prove it. Various conspiracy theorists, hackers, researchers, and political pundits made their attempts but none truly showed what was promised to be revealed by their research.
Things are much different in the conspiracy theory space. Evidence is, well, not required.
In the summer of 2019, on various social media posts, blogs, and conspiracy websites, SCYTL’s foreign operations came into prominence among election fraud conspiracies. Tales of how SCYTL was manipulating U.S. elections by sending the votes overseas to be tabulated and then sending them back to the U.S. as manipulated results began spreading. At the time, I was monitoring various election fraud conspiracists on social media as part of my normal activities. On 8 NOV 20, the first Raid on SCYTL Server in Germany post crossed my feed.
The Hunt Begins
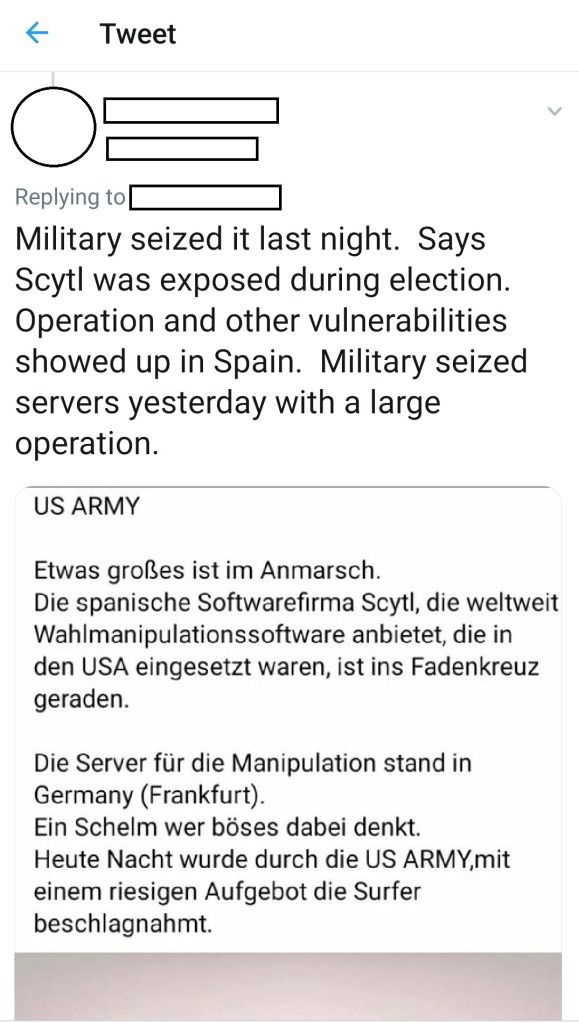
This tweet’s screenshot doesn’t show the date and time so here is another view.

I have chosen to redact the accounts associated with these Tweets so as to not amplify their message and give the users more attention than they already have.
By 12 NOV 20, the Raid to capture the SCYTL server conspiracy had spread as far as the U.S. Congress. On that day, during an interview broadcast on Newsmax TV, Congressman Louie Gohmert told interviewer Chris Salcedo that the U.S. military had seized the SCYTL server and that all of the election fraud evidence would be found there. Asked about his source for this information, Gohmert replied it was, “A German Tweet in German.” By this time, conspiracy theorists and a variety of far-right organizations were convinced President Trump had lost his bid for reelection only by crimes committed by the deep state and possibly Satan. Now, an actual member of Congress was openly amplifying the conspiracy theory. It was a shot in the arm for the fringe movements associated with Qanon.
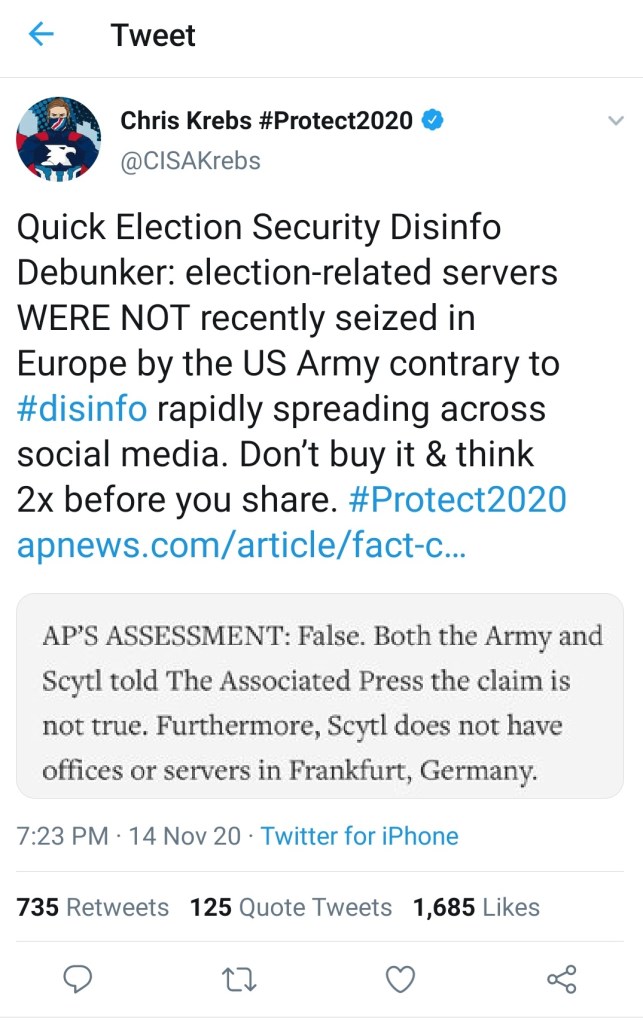
The Raid Conspiracy had spread so far and so fast that within two days, media outlets, SCYTL itself, other election companies, and the Director of the Cybersecurity and Infrastructure Security Agency (CISA), Chris Krebs, were compelled to address it. President Trump would fire Mr. Krebs three days later, seemingly for not going along with the stolen election lie.
As is the case with most conspiracy theories, debunking them does not make them die. During the final week of November 2020, retired Lieutenant General Tom McInerney, himself no stranger to kookie conspiracy theories, told a new version of the Server Raid story; a version in which an actual firefight broke out during the raid between U.S. military forces and the CIA operatives who were inexplicably protecting the systems that stole the election. Later variations of McInerney’s version would go on to claim that Gina Haspel, then Director of the CIA, was wounded, or possibly killed, during the SCYTL server raid in Frankfurt.
Although the conspiracy theory was ubiquitous at the time, no one, conspiracist, debunker, or otherwise, had traced the theory to its origins. Never one to turn down a challenge, I took it upon myself to do so.
It Didn’t Take As Long As You’d Think
The first problem I encountered was that the majority of posts about the SCYTL server story were not written posts with links attached to where the poster had found it. People from all over the world were sharing a screenshot of other posts minus any links or references. They weren’t even giving anyone credit for the post. I found this strange. It was as though it was being done intentionally in order to conceal the origins of the screenshot.
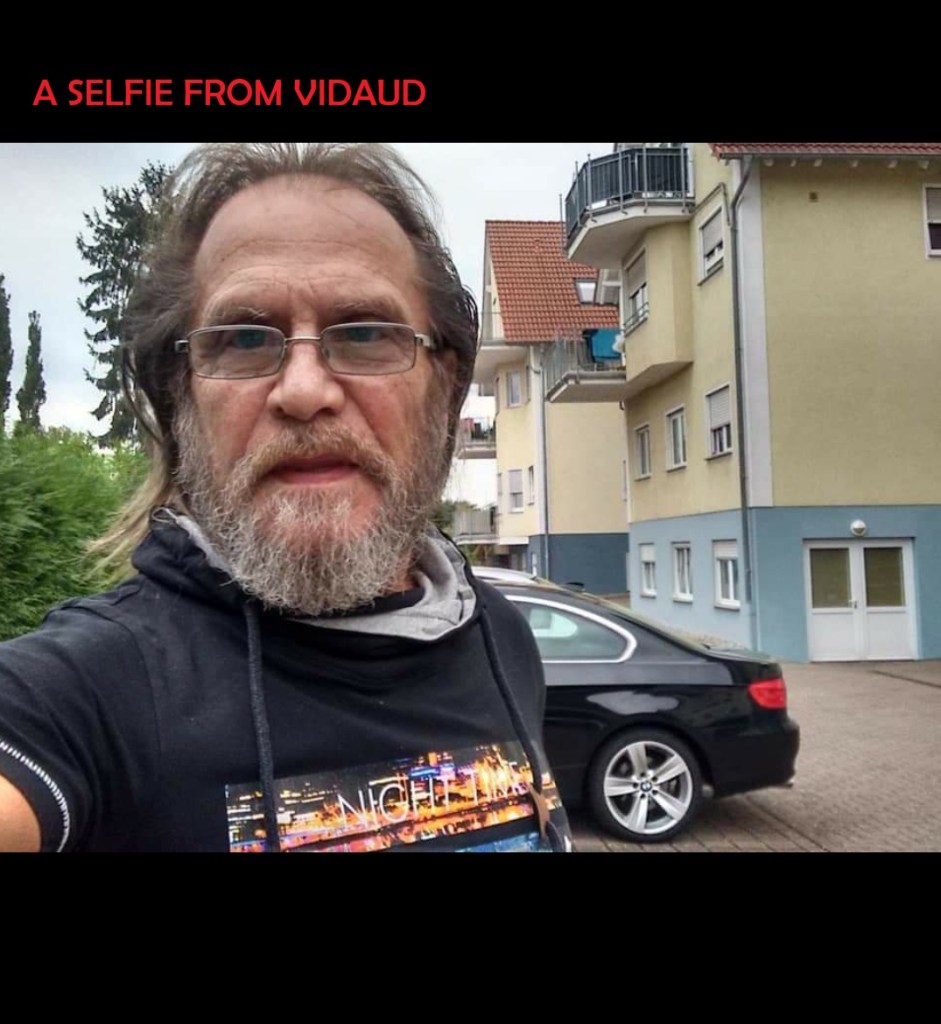
Image searches and other methods turned up thousands of posts about the story and there were an equal number of images returned. It was just a matter of sorting through the information looking for further clues. A couple of hours into my research sorting the images of the screenshot, I discovered a screenshot of the screenshot that also included the last couple of lines from the person who posted it. In that line, text was present stating, “from my good friend, Vidaud.”
With the name Vidaud added to my previous searches, as well as adding the first line of text in German, I was able to find the person on Facebook who posted the SCYTL story for the very first time. I went through a significant amount of research and verification of my findings in order to feel confident that this person, going by the name Louis Alberto Fernandez Vidaud, was the origin of the raid story. No references to this story were located across the internet prior to this post.
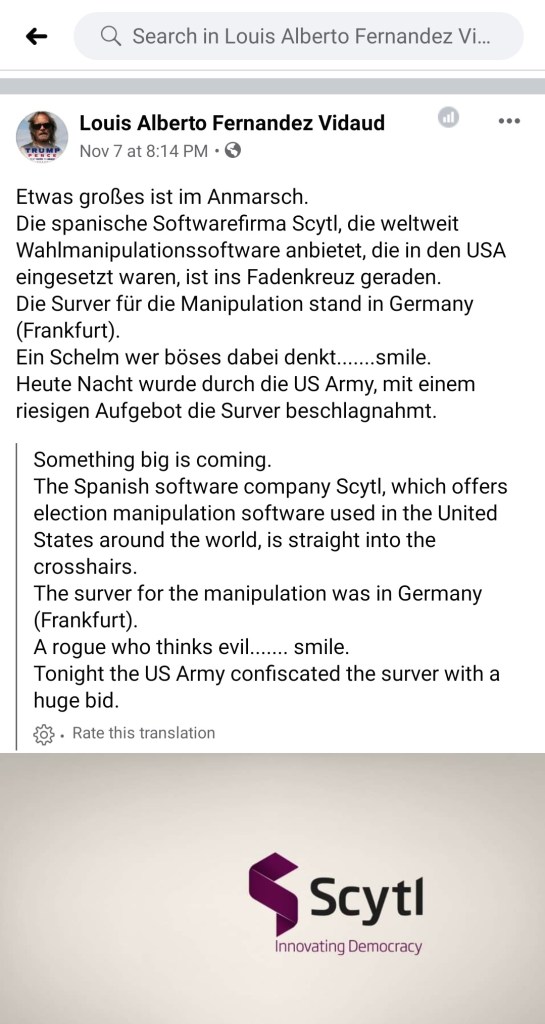
Vidaud created the Facebook post on 7 NOV 20. Within a day, the post had been modified and the words US ARMY began showing up above the original text, as seen in the first screenshot posted in this article. English versions followed that were not the same text as the poor translation provided by Facebook’s system. I had found the source of the social media post.
Vidaud and His Not-so Unpredictable Associations
Digging into the man calling himself Vidaud was limited to his public Facebook posts and uploaded photos. His Facebook account has been removed so if he is still on social media, he has built a new profile most likely with a different name. Regardless, Vidaud is an interesting character, to say the least.
Vidaud’s Facebook account, which described him as a truck driver and this seems to be confirmed based on photos he posted to his account, was filled with very hard right-wing politics, antisemetism, and, probably most predictably, pro-Russia propaganda. There’s no need to go into Vidaud’s entire social media presence but I thought it important to include a few screenshots taken from his page. The all-caps text in red was added by me.
If you are unfamiliar with the beanie-wearing, tattood tough-guy seen in the last photo gallery, his name is Alexander Zaldostanov. He is the leader of the Russia based motorcycle club/mercenary army called the Night Wolves, a Russian Nationalist group that is widely known to be a proxy force for the Kremlin. The Night Wolves were directly involved in Russia’s operations in Crimea and eastern Ukraine.
Discovering that the origins of the SCYTL server story was most likely sent out into the universe courtesy of a Russian disinformation campaign was something I was willing to accept. I’ve found no other explanation to date.
As mentioned earlier in this article, the information linking SCYTL to a network server in Germany, and subsequently confirmed by SCYTL itself, had been established prior to the raid story hitting the conspiracy spaces. It had been on the internet for more than a year and a half before being turned into a harrowing story of patriotic operators and treasonous deep state operatives. I first saw reference to it in the summer of 2019. I was soon to discover the connections between SCYTL and the German server predated that as well.
The First Strands of a Violent Web
After the mid-term elections of 2018, stories of suspected voter fraud and election tampering were spreading across conspiracy media and legacy media alike. It was nothing new. Since electronic voting options have become a part of our election process, suspicions have been openly discussed by all sides of the political debate. In fact, between 2012 and 2014, the most prominent voices calling for investigation of election irregularities were members of the democrat party, not the far-right personalities making the same accusations today. Some of those suspicions could be valid but that is not the subject of this report. A simple Google search of the subject will provide you with plenty of resources to study if you so wish.
In 2017, a new company emerged from an aircraft hangar in Texas. ASOG, known as Allied Special Operations Group at the time, has a complicated history that was expertly laid out in a Washington Post piece on 9 May 21 titled – The Making of a Myth.
ASOG entered the election fraud research arena in 2018 and its employees began researching the subject and issuing reports. Their work in this field led me to a familiar name.
Enter The Spyder
Josh Merritt, who was a part of ASOG until November of 2019, came to prominence as one of the affiants who provided detailed information to Attorney Sidney Powell for her “Kraken” election fraud lawsuits following President Trump’s failed reelection bid. The Washington Post, which has been out front in much of the important reporting since the November 2020 election, “unmasked” Merritt as the person behind one of the anonymous affidavits Powell submitted as evidence.
Josh Merritt was also the researcher who located SCYTL’s server in Frankfurt, Germany.
While performing his duties for ASOG, Merritt conducted various route tracing investigations related to the major election companies, specifically Smartmatic, SCYTL, and Hart. Merritt’s research identified the SCYTL server and, according to Merritt himself, his research was added to existing ASOG research that was being presented to political figures and donor groups.
Since SCYTL confirmed the use of the Frankfurt server during 2019, the time period during which Merritt conducted his research, it appears Merritt’s work identifying the server was accurate and reliable. SCYTL also admits that this server was no longer in use in 2020, which explains why no other researchers during that year could reproduce Merritt’s results. It also puts the lie to any statements that SCYTL housed U.S. votes on a German server during the 2020 election.
During a lengthy interview with Merritt, he expressed regret that his research was misrepresented by those who manipulated it, added to it, and combined it with bogus conspiracy theories in order to better sell their story to the media and the conspiracy crowd. Merritt stands by the accuracy of his 2019 research.
Merritt expressed a belief that some of the more elderly members of the conspiracy crowd, namely former generals and congressmen, simply confused and conflated the avalanche of information that was being passed to them and they blurted it out thinking it was the story they had been told when, in fact, it wasn’t. How a Facebook post by a German truck driver made its way into the hands and minds of our elected officials and was accepted as absolute truth is anyone’s guess.
It is unfortunate that sensationalizing an actual finding can lead to the wild conspiracy theory that Delta Force Operators and CIA Officers were killing each other as they fought over a computer server but that is the state of the world today.
I will consider this the definitive, and final, report on this particular conspiracy theory. The originating Facebook post was successfully located and the origination of the information indicating a SCYTL server in Frankfurt, Germany has also been confirmed. This serves as a very good illustration of how these theories mutate and metastasize as the plague of their disinformation spreads.